Cracking the code: How 'Malevolent Duration' shapes your company's cybersecurity success
By Wilson Chua
In today’s technology-driven business landscape, maintaining robust IT and security operations is paramount to safeguarding sensitive data, customer trust, and overall business continuity.
As a non-technical company leader, it’s crucial to have a grasp of key metrics that quantify the effectiveness of your IT and security efforts. How can YOU measure your IT or Security Team’s effectiveness?
I suggest we start tracking “Malevolent Duration.”
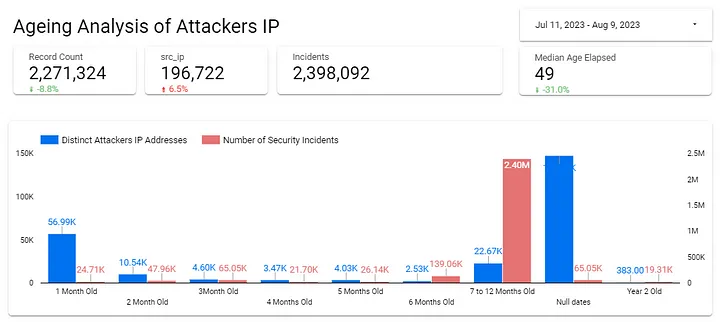
In our case, we apply this measure against IP addresses that are seen attacking our network. In the chart below, we simply bin the attacking IP addresses based on how long they have been seen attacking us.
What is Malevolent Duration?
Malevolent Duration refers to the amount of time that malicious activities, such as cyberattacks or security breaches, persist within an organization’s network or systems BEFORE they are resolved. Basically, it measures the effectiveness of your security measures in detecting and responding to threats promptly.
Why Malevolent Duration Matters?
As a company head, understanding the significance of Malevolent Duration can provide valuable insights into your organization’s security posture and operational efficiency:
1. Real-world Threat Reflection
Malevolent Duration directly reflects the extent to which your organization is vulnerable to potential cyber threats. A shorter Malevolent Duration indicates that your security measures are effectively identifying and neutralizing threats, reducing the window of opportunity for malicious actors to exploit vulnerabilities.
2. Risk Mitigation
Longer Malevolent Durations can signify potential gaps in your security defenses. The longer a hacker has access to your systems, the MORE damage they can do. The remediation costs is also likely to be higher the longer they have such an access.
By monitoring this metric, you can identify areas where your organization’s defenses might need reinforcement, enabling you to proactively address weaknesses before they can be exploited.
3. Incident Response Efficiency
Measuring Malevolent Duration helps evaluate the efficiency of your incident response processes. A quick response reduces the potential impact of security incidents, minimizing potential financial losses, reputational damage, and legal implications.
4. Resource Allocation
Analyzing Malevolent Duration can aid in optimizing resource allocation. By identifying recurring patterns in threat persistence, you can allocate resources to the areas that require stronger security measures, enhancing the overall effectiveness of your security strategy.
5. Compliance and Regulations
Many industries are subject to strict compliance regulations concerning data protection and security. Monitoring Malevolent Duration can help demonstrate to regulatory bodies that your organization takes security seriously and is actively working to minimize the impact of potential breaches.
6. Business Continuity
Effective IT and security operations contribute to uninterrupted business operations. A shorter Malevolent Duration reduces the likelihood of prolonged disruptions due to security incidents, ensuring smooth business continuity.
How to shorten Malevolent Duration
To reduce Malevolent Duration and enhance the effectiveness of your IT and security operations, consider implementing the following strategies:
1. Continuous Monitoring: Utilize advanced threat detection systems that provide real-time monitoring and alerts for suspicious activities.
2. Incident Response Plans: Develop and regularly update comprehensive incident response plans to ensure swift and effective action in case of a security breach.
3. Employee Training: Educate employees about cybersecurity best practices to minimize the risk of human error leading to security incidents.
4. Patch Management: Stay up-to-date with software patches and updates to mitigate vulnerabilities that attackers might exploit.
5. Threat Intelligence: Stay informed about the latest cyber threats and attack techniques to proactively adapt your security measures.
Remember:
1. Malevolent Duration is a valuable metric that provides insights into the effectiveness of your IT and security operations.
2. By monitoring and reducing this duration, you can enhance your organization’s resilience against cyber threats, minimize potential damages, and demonstrate a commitment to data protection.
3. As a non-technical company head, understanding and tracking this metric can play a pivotal role in ensuring your company’s digital assets and reputation remain secure. What you measure is what you get!